Latest News and Resources
7 Reasons You Might Switch To Windows 10 This Year
7 Reasons to Switch to Windows 10 This Year
Windows 10 (Win10) is the next generation of Microsoft operating systems.
1. Free for a Limited Time
If you currently have computers with Windows 7 or Windows 8.1, then
2. The Start Menu
When
3. Re-Sizeable Apps
You can now re-size apps that were previously full screen-only as if they were
4. Virtual Desktops
Windows
5.
With this
6. Futuristic Biometrics
Windows Hello is a brand new,
7. Tons of Customization
Microsoft has gone from clunky and
Key Raider Malware Targets Apple iOS Devices: What is it? Who is is affected? Should I worry?
KeyRaider Malware Targets Apple Devices

This week Palo Alto Networks announced their identification of the KeyRaider malware attack, “the largest known Apple account theft caused by malware,” which to date has compromised the IT security of over 225,000 Apple accounts.
How Does KeyRaider Work?
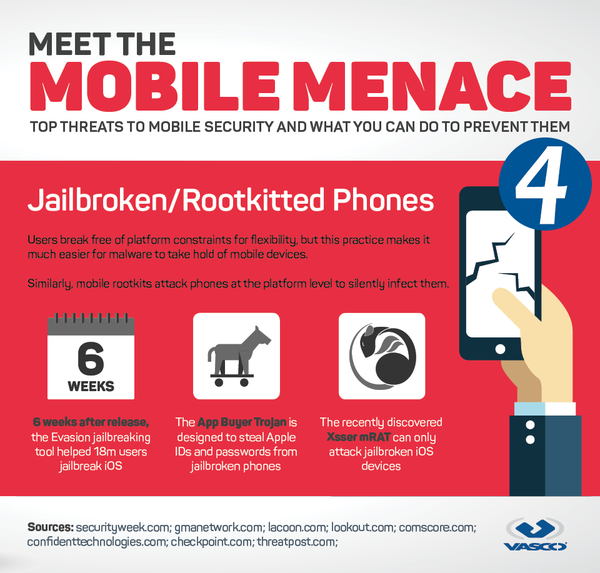
KeyRaider targets “jailbroken” iDevices, which strips Apple devices of their built-in security measures.
Why would someone “jailbreak” their device? There are a variety of reasons users may choose to “jailbreak” their devices ranging from using banned apps to customizing control centers, but typically the reasons all boil down to wanting to use prohibited downloads or running programs which are not allowed by Apple.
By focusing in on exploiting jailbroken iPhones, KeyRaider is able to: Scrape sensitive account information and steal iTunes usernames, passwords, and sensitive payment information.
Furthermore, KeyRaider is believed to steal Apple push notification service certificates and also to disable native and remote unlocking functionalities on iPhones and iPads.
According to Stephen Coty, the chief security evangelist for Alert Logic, this means that KeyRaider can “lock your phone very similarly to ransomware that has been plaguing many individuals across the world.”
Two iOS Jailbreak Tweaks Leading to Disaster

Throughout their research, WeipTech and Palo Alto Networks identified two iOS jailbreak tweaks which are believed to have stemmed from the popular jailbreaking tool, Cydia.
The tweaks were then downloaded over 20,000 times and have compromised the sensitive information of users across 18 countries in the attack on more than 225,000 accounts.
Should I be worried? What does KeyRaider mean for my organization’s IT security?
Once More: If you do not have any jailbroken iOS devices in use, your organization is safe from KeyRaider.
If you are worried about having any sensitive information from your business being compromised by KeyRaider, the first thing you need to do is check that your organizations’ users do not have any jailbroken Apple iPhones or iOS devices in use.
Establish Policies: Prohibit Any and All Jailbroken Device Use Within Your Organization
Throughout this process, make sure to remember that KeyRaider’s success or failure relies on user victims having “hacked” their own iPhones first.
By jailbreaking iOS devices, users directly open the door to threats such as KeyRaider to compromise accounts.
It’s Safe to Say: Don’t Stay Silent
At the same time, your employees and office users must know that they are safe to report that they have a jailbroken device in use.
Otherwise, without the promise of “safety” you could suffer the consequences of a KeyRaider attack due to users staying silent, devices going unreported, and accounts being exploited.
How can I check if there is a jailbroken iPhone or iOS device in use at my organization?
Unsure if you have any jailbroken devices in place? It may be time to conduct an IT asset inventory.
If you work with an IT services provider, chances are, they already have a detailed inventory technologies and devices with access to and being supported for your business.
IT Security Is Not A One-Off Engagement
Remember, the success of your information security, IT support and ongoing technology improvement programs all require buy-in from your users.
If your people have have never seen your company’s IT policy, employees have no idea of what security best practices are or your organization still needs to be setup to facilitate ongoing updates and regular system maintenance, it may be time so seek out professional IT support services.
Feel like you need to double-check?
Reach out to your San Francisco Bay Area IT services provider to have our local helpdesk team perform a free network assessment of your business IT environment.
Instead of allowing your technology to suffer, keep your users safe from the latest malware and ransomware attacks by having full team of IT specialists ready to answer your questions and solve your problems today!
Read More
Still Stuck on Windows Server 2003? Get Your Business Back on Track
Survival Steps After Windows Server 2003 End of Support
On July 14, 2015, Microsoft stopped providing extended support for Windows Server 2003 (WS2003). Ending this support meant no more security updates or incident support for customers who retained the older operating system.
While this change didn’t cause everyone’s computer to suddenly stop working, implode or jump the track, it does mean that over time, both security and safety could be compromised. It also means that if you are still using WS2003, some changes need to be implemented to ensure that your company remains safe, secure and compliant.
Change In Product
WS2003 has undergone a number of changes since its release in April 2003, including two major updates in 2008 and 2012. However, many companies did not upgrade. An AppZero Study reported that more than 10 million computers were still using WS2003 just prior to the cessation of all support. Some of their reasons for retaining WS203 were:
- Lack of urgency for switching operating systems as long as Microsoft continued to offer support for WS2003
- Difficulty modifying customized or packaged applications software to the new operating systems
- Financial concerns, i.e. cost of upgrading existing system and software
What If It Still Works?
Although your computers and businesses will continue to function, problems will accumulate over time.
For instance, lack of security updates leave your system vulnerable to new viruses or inventive hacking.
Power outages may mean crashed systems, lost data and impossible recovery.
Existing software applications may no longer function or be available as companies adapt to the newer operating systems.
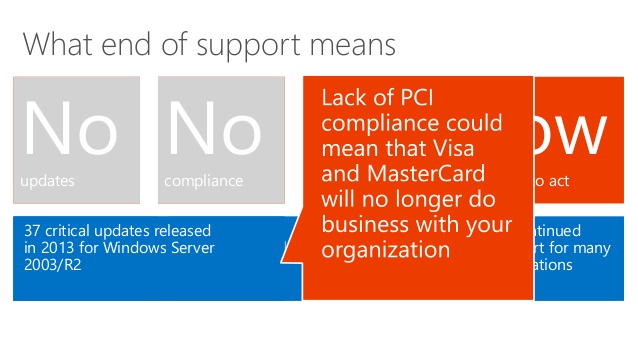
And for organizations tied to compliance regulations (such as healthcare and HIPAA or businesses who deal with credit card information and PCI), compliance issues will emerge sooner rather than later.
Furthermore, simultaneously putting your business through a server migration in addition to a compliance assessment can put your business operations at risk as the demands on your internal resources spikes and accelerated deadlines are being enforced by auditors, industry regulators or your clients themselves.
Instead of placing your organization under the gun of tight timelines to hit a compliance assessment date, get started now to make sure your your migration is built to last.
What To Do
There are steps you can take to keep your computers — and your business — running while you migrate to a new operating system. Ed Tech Magazine recommends the following actions:
- Step 1: Conduct an assessment and determine which applications are still running on Windows Server 2003.
- Step 2: Prioritize your applications by importance and ease of transition.
- Step 3: Test your applications with free trials of newer platforms before purchase.
- Step 4: Build a migration plan.
Get Help
If these steps seem overwhelming, your Bay Area IT support specialists at Bay Computing have years of experience and are available to help your organization avoid complications and safely navigate the transition.
Instead of struggling through the process alone and running the risk of prolonged downtime, let our team architect your implementation plan, complete your migration and test your applications to make sure your systems are configured to perform optimally and to help you avoid future business interruptions.
One Stop Shop for Small Business Server Migrations
Our team of experts can help you get started by conducting your free onsite network assessment and then help prioritize your needs throughout each step of the the migration as they work with your team to develop a thorough understanding of how your team uses each specialty application.
You invest in technology to help improve your business operations. Make sure your business continues to run uninterrupted as you run your company and accomplish your goals, all while strengthening and moving your IT infrastructure into the future.
Don’t wait until disaster strikes or a deadline is looming. Contact your Bay Area IT support specialists and get your business back on track today!
Read More
Healthcare IT: Addressing Challenges of Information Security
![Healthcare IT HIPAA EHR Management Support Healthcare IT HIPAA EHR Management Support]() Information Security: What’s It Mean for Healthcare IT ?
Information Security: What’s It Mean for Healthcare IT ?
The pervasive use of Electronic Health Records (EHR) has made sharing patient information significantly easier. While this has dramatically improved the quality of patient care, how secure is your confidential patient information?

Information Security in Health Care
The goal of EHR is to collate information for better patient care and encourage smarter spending. But what happens when patients are wary of the accuracy and confidentiality of their EHR? They may refuse to divulge information crucial to getting proper medical care.
Security Breach Risks
Ideally, healthcare IT should be an invulnerable fortress. But is it really? Let’s take a look at the weak spots that need improved fortification.
Endpoint Encryption
According to this Forrester report, several healthcare organizations get by on a miserly security budget, and only 43 percent of healthcare firms have a comprehensive data security budget. As a result, securing endpoint data does not get the priority it should. Very few healthcare organizations use file-level or full-disk encryption.
Hackers
Progressive technology is a breeding ground for sophisticated hackers. Hackers are more interested in financial fraud and identity-theft-related data, such as a patient’s social security number, than health-related information. In fact, recent months have seen a 600 percent increase of such attacks.
Healthcare Workers
Healthcare workers’ passwords are often the first breach in the battlefront of patient information security. For example, sometimes they forget to log out of their work station. Such mistakes lead to about 25 percent of security breaches, including identity theft and access to patient information records. Unless employees are given adequate security training, all security revamps will only be wasted effort.
Bring Your Own Device (BYOD)
BYOD permits healthcare employees to access work data via their personal devices. This trend adds a whole new dimension to patient health information security. Without an inclusive, operable and strictly followed security system in place, BYOD is the equivalent of encouraging a jewel thief to gate crash a celebrity wedding.
Business Associates (BA)
Most external threats to patient information security are due to the carelessness of BAs who have access to such information. They are the cause of about 20 percent of recent security breaches.
The Technology-Expertise Gap
Often, even if healthcare organizations have the budget to implement the right technology to detect pitfalls, the security technology remains unexploited because most in the organization are not trained and equipped to implement it.
The key to countering security threats, whether external or internal, is awareness and training. Training should be an ongoing process in order to address changes in technology and new threat sources.
Read MoreWindows 10: Helping Your Office Bridge the Gap Between PCs and Tablets
Windows 10: Helping Your Office Bridge the Gap Between PCs and Tablets
When
Universal Apps
Apps from the Microsoft App store
Redesigned User Interface
One of
Seamless Tablet Mode
Some of the
Windows 10 learned many lessons from Windows
How An Excellent IT Workflow Will Keep Your Business Running
Elect
Hire
Why
iPhone, iPad and iOS Fall Victim to YiSpecter Malware Attacks
Everyone was YiSpecter Fighting, Those Hacks Were Fast as Lightening
Your “how to” blog post should teach the reader how to do something by breaking it down into a series of steps.
Begin your blog post by explaining what problem you are going to solve through your explanation and be sure to include any relevant keywords. Add in a personal story to establish your credibility on this topic. And make sure to end your blog post with a summary of what your reader will gain by following your lead.
Need some inspiration? Check out these “How-To” examples from the HubSpot blog:
- How to Write a Blog Post: A Simple Formula to Follow
- How to Do Keyword Research: A Beginner’s Guide
- How to Write an Effective Meta Description (Yes, They Still Matter)
BODY:
Now deliver what you promised in the first section. This is the longest part of the post, so make it easy to read. Use short paragraphs, bullet lists, and bold headings to set different sections apart.
Some common section headers include:
Step 1: Getting Started
Step 2: Do Your Background Research on…
Step 3: First Steps for…
Step 4: Analyze and Repeat
Step 5: Wrapping Up
You can use bulleted lists, numbered list, or multiple headings. Include as many steps, numbers, or bullets that will allow you to discuss your topic thoroughly.
Here are some pointers to make the best possible body of your blog:
- Include visuals
- Include short explanatory phrases in your headers
- At the end, transition into your conclusion
CONCLUSION:
Now it’s time to say goodbye and wrap up your post. Remind your readers of your key takeaway, reiterate what your readers need to do to get the desired result, and ask a question about how they see the topic to encourage comments and conversation. Don’t forget to add a Call-to-Action to turn your blog post into a marketing machine!
Congratulations! What a lovely how-to post you’ve created.
Read More
Experts Finding Malware Creativity Advancing Faster Than Ever
Experts Finding Malware Creativity Advancing Faster Than Ever
How many technology solutions does your business rely on? Integrated software packages, softphone-based VoIP systems, productivity enhancing smartphones — technology has transformed workplace productivity, but it comes with a dark side. Malware, which is malicious software such as viruses and trojans, continue to be a major problem. One anti-virus software company detected 2,205,858,791 attacks in Q1 2015.

As more businesses gather sensitive data stored in on-premise and cloud-based tech solutions, the malware attacks become more sophisticated. User computers, network infrastructure, and mobile devices are all viable attack vectors for a creative cybercriminal. Once your computers get infected, the direct and indirect costs can be enormous, and you might not even know how the malware got in. Here are two of the most creative, and most dangerous malware threats to the business world.
Cryptowear
What would happen if you lost access to mission-critical parts of your business system for a day? A week? Cryptowear is one of the latest malware trends. It locks down essential parts of a system and demands payment before you can use the system normally again. In many cases, these applications look like legitimate software prior to launching the attack. If you don’t pay up, you’re going to need to go through a lengthy backup restoration process to get everything back to normal.
Malware App Mods
Does your business have a bring your own device (BOYD) policy, where employees can use their own personal mobile devices for business purposes? If you do, you could be inviting all manner of malware into your network. One of the latest mobile malware trends are apps that offer modification or cheat codes for popular mobile games. The user downloads and installs the mod app, which actually contains malware. If it’s not detected early, the infection could end up hitting your entire business network.
How to Protect Your Business From Malware
So how do you stay a step ahead of the cybercriminals? The right IT security safeguards and solutions go a long way to staying on top of potential attack vectors. A technical support provider gives you the ability to use your resources to get the knowledgeable help you need to handle IT security issues.
Need help with keeping malware from ruining your business? Contact us for all your Bay Area IT services needs, whether you’re fighting an active malware infection or you want to proactively handle issues.
Read More3 Ways to Grow Your Business With IT Services
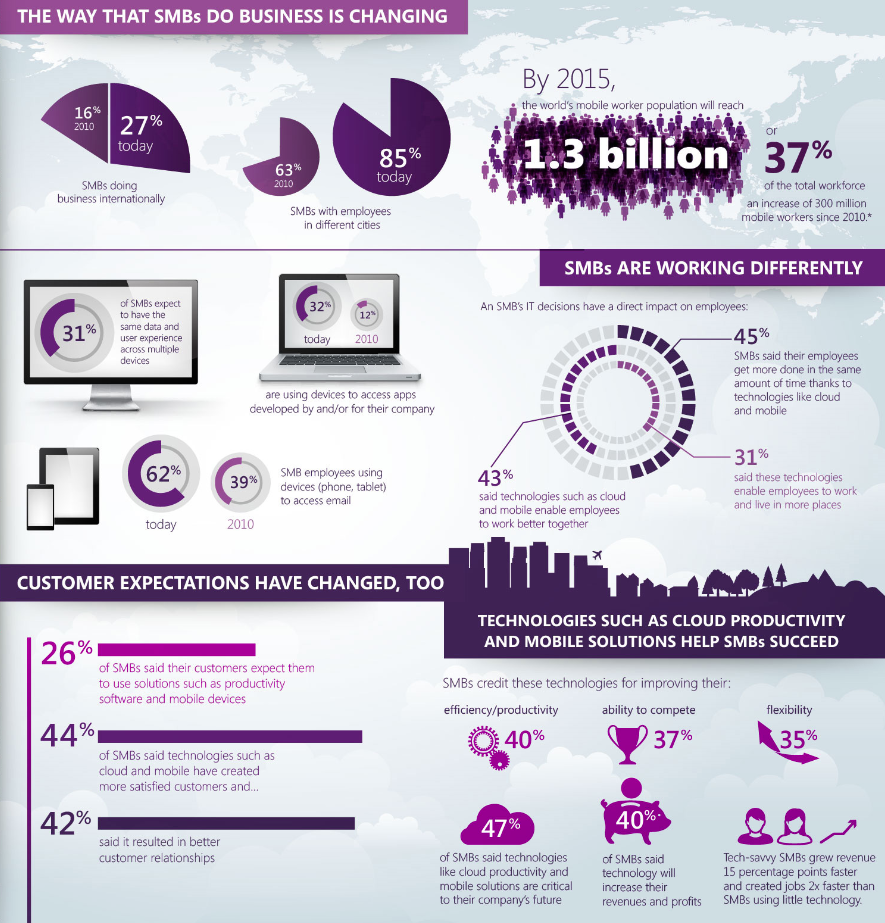
Want to kick-start new business leading into 2016? Enable growth with best-in-class technology and IT Support Services
42 percent of small businesses have no IT department, yet many of these businesses rely on technology-based solutions to fuel their future growth. Without dedicated IT professionals, business owners or other critical personnel are regularly pulled away from their core business responsibilites to address ongoing IT issues.
Your business can’t grow if you’re constantly running around and putting out fires, but you aren’t at the point where your budget supports having a full-time technical staff. It’s time to consider the ways San Francisco IT support helps your business grow over the long term.
1. Cost-Effective Technology Procurement
You know what processes you deal with on a day-to-day basis, but you don’t have time to read up on every technology business solution available to figure out which options make the most sense for your company.
If you sit down to do the research yourself, you take time away from your actual business duties. IT Services Bay Area helps you identify your business work flows that benefit most from technology, locates the best vendors for these options and helps you with the procurement and deployment process.
Think of the IT service as a trusted friend who knows all about the hottest restaurants in town, and exactly what to order off the menu to suit your tastes.
2. Proactive Maintenance
You don’t think about what could go wrong with your IT infrastructure—until it’s your busiest day of the year and all of your mission-critical business systems are down. Instead of ignoring small problems until they snowball into major blows to your business growth and finances, using IT services for proactive maintenance keeps your infrastructure stable and strong. If you take your car in for its regular oil change, why wouldn’t you get systems looked at when they’re critical for your business success?
3. Leveraging IT Expertise
Let’s face it: As a business owner who isn’t working in a technology sector, you don’t have time to stay up to date with IT best practices, the latest threats, company-changing innovations and other tech-based business intelligence.
You need the ability to put this information to use to stay competitive without dealing with the overhead costs associated with brining on a full-time IT employee. Some days you only need simple troubleshooting, other emergencies may require a full technical support team.
When you partner with a Bay Area IT support services provider, you leverage their entire team’s expertise so your business stays on top of the latest threats and trends, and is provided with a cost-effective method of handling your IT needs and creating a solid foundation for your future business growth.
San Francisco IT support goes far beyond simply providing helpdesk technicians to fix technical problems as they occur. With the right managed services provider, your organization helps you design, implement and create a technology foundation for fueling your business success.
When you keep your IT systems healthy and functioning at peak performance, you continuiously build upon your competitive advantages and improve your opeational capabilities to help blow your completition away.
Read More5 Pervasive Myths About Cloud Computing
Businesses in the United States spend well over $13 billion each year on cloud computing services. As “Cloud” picks up steam as the latest buzzword, migrating to the cloud is no longer an expensive, risky venture reserved only for major enterprises.

With prices continuing to drop as the technologies develop and mature, the latest studies are finding that companies with fewer than 19 employees are now 20 times more likely to adopt cloud technologies than their larger competitors.
The Lay of the Land
The hybrid cloud, a mix of public and private cloud computing options, is a new choice that’s growing quickly in popularity. Gartner predicts 50 percent adoption by 2017 of this flexible and secure option. Despite the fact that cloud is a quickly growing choice, there are some pervasive myths surrounding it:
1. The Cloud Is Insecure
Modern organizations are rightly concerned about cybercrime leading to costly data breaches. However, Gartner highlights that the idea that cloud is less secure is based on a “trust issue,” and not necessarily fact.

As with any other major technology investment, when considering cloud services, proper due dilligence is necessary to confirm that appropriate security has been implemented. That being said, many cloud providers are not only aware of common information security concerns, but proactive in their approaches to cybersecurity.
In many cases, as an additonal assurance to their customers, cloud providers will voluntarily undergo a number of industry security and compliance audits, such as PCI-DSS and SSAE 16 SOC 1 and SOC 2.

Furthermore, for those companies who feel more comfortable with a tighter control over their organization’s security, it should be noted that both cloud computing and hybrid cloud solutions can provide critical protection for small and medium-sized businesses (SMB).
2. Cloud Solutions Are Inflexible
There are some cloud vendors that are highly inflexible; these companies may demand high penalties for service termination or upgrades. However, writer Chris Quinn reports that a large percentage of companies are turning to hybrid solutions to ensure flexibility.
This provides the choice to “deploy and consume” as needed in combination with more traditional solutions. In many cases, San Francisco and Bay Area offices have found hybrid options to offer the “best of both worlds.”
3. The Cloud Is Virtualization
Virtualization can be used to provide cloud computing, but they’re not one and the same. The cloud can offer distinct advantages, including automated management, distributed control, and scalability. Additionally, there are certain security and end-user benefits tied to the cloud above virtualization, making it a more popular choice for both SMB and major enterprises.
4. Cloud Implementations Are Painful
Much like any technology solution, cloud implementations have both pros and cons. Companies that opt to entirely outsource their cloud to an out-of-the-box solution are dependent on their vendor’s support (or lack thereof), rely on vendor security measures for protection, and may face uncertain periods of downtime. Depending on the solution and organization selected, being locked-in long-term to a suboptimal solution can accidentally become your reality.
However, there are significant advantages to cloud implementations, which can include increased storage capacity, efficiency gains, and cost savings.
By working with your IT services provider, your organization has easy access to dependable cloud computing technical support while also having the advantages of cloud technologies at their fingertips. With the right technical support team, implementing cloud-based technologies can be far less painful than you have ever anticipated.
5. Working With the Cloud Must Be “Mysterious”
Many people who are new to cloud technologies believe that incorporating cloud options translates into an automatic lack of transparency.
But hybrid and private cloud deployments can offer total transparency to users, particularly when technology teams work with your organization’s office end users to help them understand their technology infrastructures clearly and fully.
