Latest in Malware: eFast Browser Attacks with False Google Chrome, Traps Users with Adware
Latest Malware Attack Replaces Users Chrome Browsers Entirely by Bunding with Legitimate Software Downloads
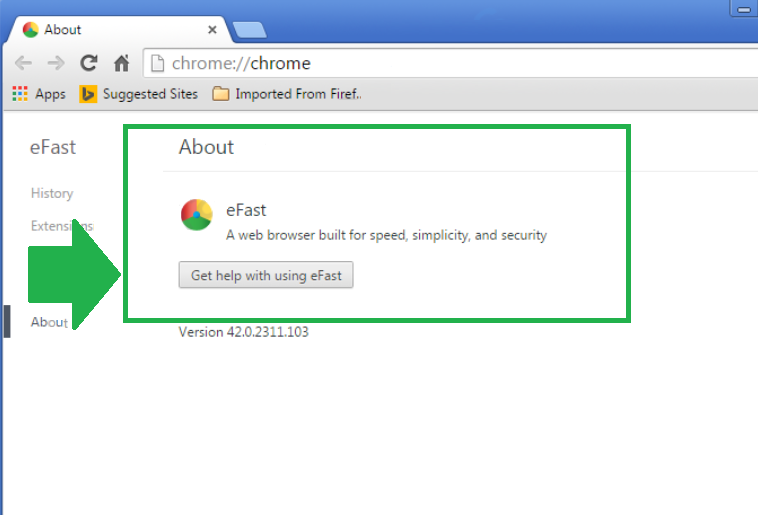
Just last Friday, Malwarebytes announced the discovery of the eFast hijacking scam which boldly attacks by replacing users’ default Google Chrome browsers with eFast, which targets victims with the promise of “A web browser built for speed, simplicity and security”
Suddenly Flooded with Pop-Up Ads? Find yourself constantly redirected to unrelated websites? It might be time to check your Chrome browser …
That being said, the malware attack acts as a stowaway within other software downloads and once it has successfully piggy-backed on a user-generated installation. But what type of installation would this be?
Have you ever had a “security software” offer to install for free or gotten a pop-up “urgent notice” that your machine needed to be scanned ASAP?
Maybe you panicked, and went ahead and clicked “yes” instead of reaching out to your IT services provider to check that the programs were actually legitimate..
What about one of those “too good to be true” free software offers (freeware) which bundle (use bundling) with the original software you were seeking with another offer promising faster online browsing or an enhanced shipping experience? We all know those little check boxes can be tricky…
Forget Taking Over, eFast Eliminates Competition
As business IT advances and office technology users become more savvy, the developers of eFast have made sure to impersonate the genuine Google Chrome browser, with an eye for attention to detail across both original Chrome icons and Chrome windows.
Instead of simply hijacking a browser, eFast specializes in erasing and completely replacing Google Chrome.
By leveraging strong user dependence on browsers and their associated functions, the developers of eFast made sure that escaping wouldn’t be easy.
As soon as eFast breaks in, it deletes all of your desktop shortcuts and taskbars to Google Chrome and replaces them with impostor links and shortcuts. From there, cybercriminals are enabled to hijack your file associations, track each of your keystrokes and and monitor each link that you visit.
![]()
Furthermore, irrelevant of which browser you start out using, eFast is set up to override program viewers for .jpg, .gif and .pdf as well as for protocols such as ftp, http, https and mailto. Basically, eFast and will force itself upon its unsuspecting users whenever they open files…And then the real fun begins as as the malware attack then injects an endless stream pop-us and ads into each of your searches…
While the unauthorized adware can generate profits for malware developers, users must also be aware that a malicious attack easily leaves your passwords, login credentials and banking information vulnerable to exploitation.
Since Google’s Chrome Team Has Been Hard At Work….
Clara Labs, the people responsible for eFast (as well as a variety of other malicious softwares such as Unico, Tortuga and BoBrowser) are now having to up their exploit strategy game with each new development.
As one critic (@SwiftOnSecurity) put it, cybercriminals and hackers are finding that, “it’s getting so hard to hijack… that malware literally has to replace it to effectively attack.”
If You Suspect You’ve Been Hit By eFast, It’s Time to Get Help Today
Being hit by a malicious attack can feel overwhelming as your business suddenly needs technical triage, is forced to decipher just what information has been compromised, and then has to remediate on a tight timeline to avoid any aftershocks or additional impact.
Getting the right IT support provider means having experts take over and stopping damages in their tracks. Instead of spinning your wheels, get your business on the road to recovery with a free onsite assessment today.



